REDMOND, Wash. — Sept. 28, 2011 — A specialized device can be a key differentiator for enterprises in industries such as retail, health or manufacturing, but the development and deployment of that device require significant time and resources. Enterprise decision-makers may think that an open-source operating system will save money. However, the real cost of a device goes beyond initial licensing to encompass time to market, customization, service and support during its lifetime, IP indemnification, and security features.
Security means more than protecting the operating system against unauthorized access and modification. Impenetrability is important, but security also encompasses the software stack, the user interface and the drivers for connected hardware. The process by which software and hardware components are updated and validated also is crucial. And reliability of the companies that provide all of a system’s components, while not technically a security element, is a vital consideration in creating a trustworthy device. A misstep in the product development process may ultimately lead to unexpected customer service problems, hamper the ability of employees to do their jobs, or expose critical parts of the enterprise’s IT system to unauthorized access.
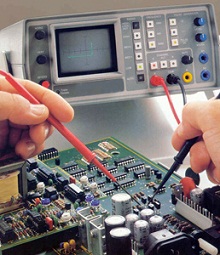
Intelligent systems enable custom development to meet specialized enterprise needs.
Yannick Chammings, CEO of Adeneo Embedded, a Windows Embedded Gold Partner with offices in France and the U.S., works with clients to create custom devices for enterprise, retail, medical and consumer implementations. He urges device planners to think beyond the immediate process of development and launch.
“Generally customers think about the operating system working on the hardware, and about the high-level app implementing the features of the device,” Chammings says. “But they forget about system mechanisms like manufacturing tests or boot tests — underlying mechanisms that make the device reliable, robust, updateable. Things we discuss include your plan for updating the software, which can be really complex if you’re making updates manually on each device.”
Chammings says system upgrades were a security consideration in a client project for a medical device that had to pass regulatory review. Critical aspects of the device’s function, including the user interface and connectivity, depended on the operating system. The client realized that with a Linux-based device, upgrades to the OS would require analysis of a vast number of existing patches available from the development community, and an insufficiently secure patch could threaten the integrity of the device. By contrast, Windows Embedded offers a regular cadence of system updates that have been tested and verified. “With Windows Embedded delivered as a fully packaged system, it’s much easier to handle upgrades as needed without taking the risk of destabilizing the whole system,” Chammings says.
A device is more than an operating system, of course; even a simple enterprise device must run applications and execute functions, and a sophisticated device may run multiple applications, interoperate across networks and receive data input. Windows Embedded enables developers to lock down the device platform so that only authorized applications or drivers can be installed or executed, thus limiting the ability of external input to compromise the function of the device or the integrity of its data. How an intelligent device integrates with an enterprise’s back-end system — for inventory tracking, order processing or accounting, for example — also raises security issues.
“Specialized devices today may often operate in open environments where potential hackers can gain access to enterprise infrastructure,” says Mark Pendergrast, Senior Product Manager for the Windows Embedded group, who recently commissioned a new Microsoft white paper that offers guidance to business and technical decision-makers. “Security at the device level, and with the device’s exposure to the enterprise systems, becomes an IT security concern.”
Such devices must incorporate not only operating system security but safeguards in the areas of software compatibility and integration, hardware robustness, and the system upgrade process. Decision-makers must consider all the points in the enterprise chain at which a system may be made vulnerable, whether through system connectivity or user decisions about how to manage access, to ensure the design and construction of a truly reliable device.
One key to ensuring that reliability is to work with an experienced device developer that has solid industry expertise and access to a wide ecosystem of partner support. A robust developer ecosystem can help ensure that enterprises can find the resources they need to develop new devices and add features to existing ones. The Windows Embedded developer ecosystem offers enterprises a variety of partners with substantial experience in specialized industry categories, helping to ensure that an intelligent device can be created in accord with any regulatory or industry standards. Developer certifications also ensure that partners meet objective standards for quality and competence.
“With open source you’re relying on freely available types of software, so you don’t necessarily have an accountable partner or company on a piece of software you’re using for original equipment manufacturing (OEM),” Chammings says. “With Windows Embedded, with clearly defined integration partners like Adeneo Embedded as part of the system, as an OEM you can have better confidence in the robustness and reliability of the solution — and with a well-regarded company available to help you.”
Business and technical decision-makers who are planning the development of specialized enterprise devices will find helpful guidance in the white paper “Specialized Devices in the Enterprise: Considerations for Deploying Embedded Devices.” The paper outlines a variety of questions that enterprises should address across the lifespan of a device, including technical and security issues and service requirements.




