Let’s face it, we have to stop using passwords
Why biometrics are best when protecting yourself online
“Cyber-crime has been identified as one of the biggest criminal threats to British business and the British economy, with available estimates suggesting the cost could be billions of pounds each year… A large proportion of the public and Small and Medium-sized Enterprises (SMEs) vastly underestimate the risk of cyber-crime and feel powerless to protect themselves against it.”
These are the words of Ben Wallace MP, current Secretary of State for Defence and former Minister of State for Security and Economic Crime – a role that includes oversight of cybersecurity and tackling cyber-crime in the UK. His quote can be found in the introduction to a report released by the UK government in March last year that laid bare the public’s misconceptions around online security.
In A Call To Action: The Cyber Aware Perception Gap, Wallace notes that there is “a widespread belief that cyber criminals focus only on big businesses and celebrities rather than ‘ordinary’ people; a misconception that there are few consequences of being a victim of cyber-crime; and an array of inconsistent advice that leads to dangerous inertia”.
This is creating a situation across this country whereby “millions of people are leaving themselves, UK businesses and UK infrastructure vulnerable by failing to follow even the most basic secure online behaviours”.
It’s a stark view of a country that’s rightly seen as a global leader in digital technology; a place that’s home to some world’s best and brightest artificial intelligence experts, videogame studios, FinTech companies and digital start-ups.
Microsoft, alone, has a cutting-edge research lab in Cambridge, data centres around Britain – including one off the coast of the Orkney Islands – and multiple videogame studios. In June, it was announced that Cindy Rose, the Chief Executive of Microsoft UK, will help lead a Government study into the competitiveness of the UK’s technology sector, to ensure the country remains one of best places in the world to start and grow a digital business.

If the UK wants to remain a global leader in technology, the efforts to attract, retain and grow companies conducting cutting-edge research must go together with developments in security. Businesses will only reach their true potential if they are secure and their customers have trust in that security.
Microsoft invests more than $1 billion in security every year. Every month the company analyses 470 billion emails for malware and suspicious websites – blocking more than five billion malicious and suspicious emails in 2018 alone – and updates 1.2 billion Windows devices.
More than 3,500 full-time security professionals work with leading artificial intelligence tools to analyse more than 6.5 trillion global signals every day. Over the years they have learned to adapt their defensive approaches through PCs to the internet era, from servers in data centres to workloads in the cloud. This has fed through to the myriad products that Microsoft makes available to consumers, meaning that Windows and Office 365 have advanced security features baked in.
It also works with other companies, organisations and policymakers to protect people across the world. Last year Microsoft joined the Cybersecurity Tech Accord, comprised of 34 technology and security firms from across the world, to “empower users, customers and developers to strengthen cybersecurity protection”.
“Within any security scenario, you’re only as strong as the weakest link,” said Brad Smith, Microsoft President, as he announced the company’s participation in the Accord. “Securing the world’s computer network requires all of us to recognize the need to increase the capability and resilience of the world’s computer networks… Protecting our online environment is in everyone’s interest.”
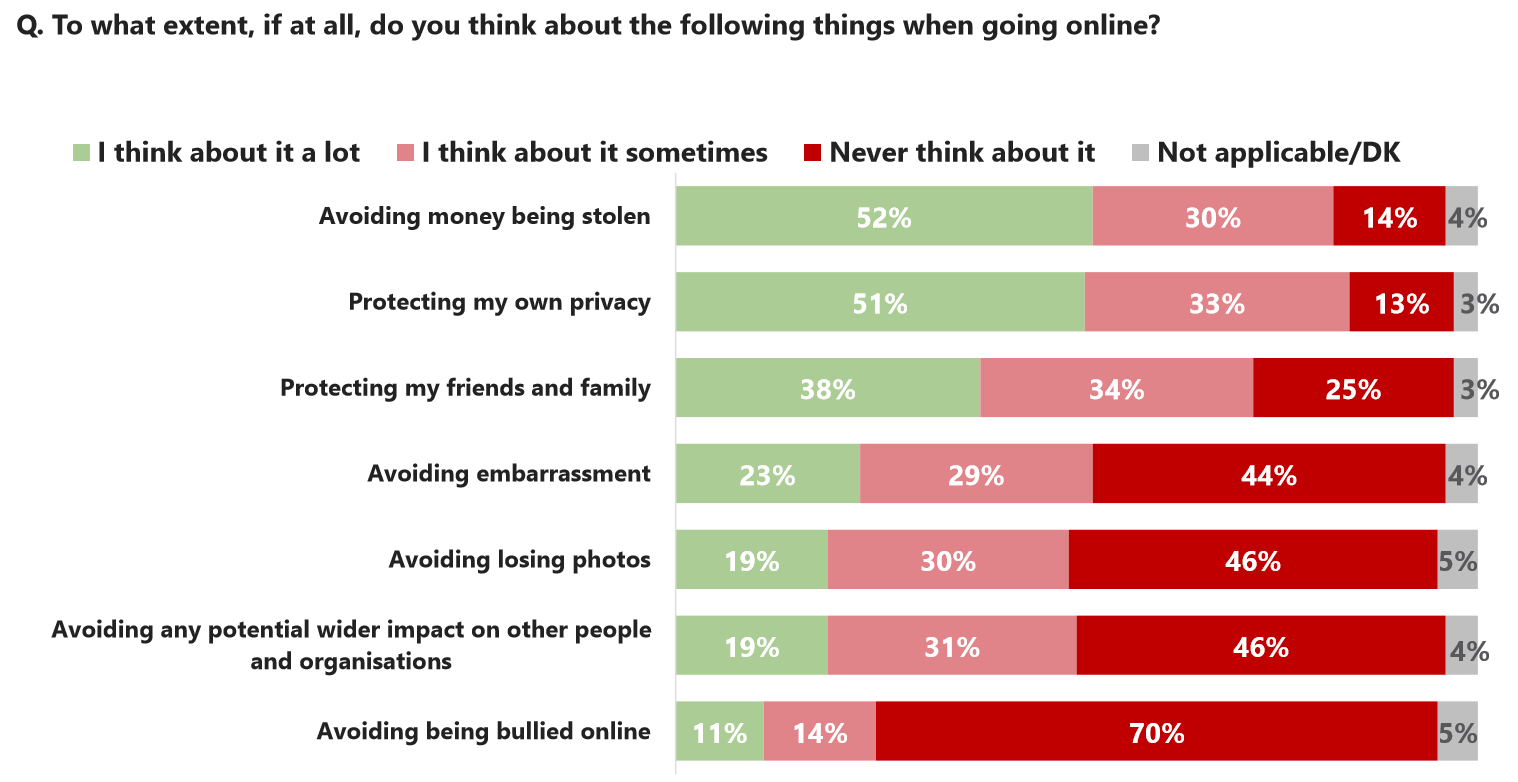
However, individuals often don’t think they are responsible for their own online security. That Government report we mentioned at the start, which used the phrase “dangerous inertia”, also found that 72% of consumers believe “it is the responsibility of companies to provide them with the tools they need to protect their privacy, security and reputation online”.
In the year to March there were an estimated 3.8 million incidents of fraud in England and Wales. Just over a quarter of those were “computer misuse offences”; and while incidents involving viruses fell (444,000), those featuring “unauthorised access to personal information (including hacking)” remained steady at 522,000.
The figures from the Office for National Statistics show that you are around 10 times more likely to be hacked than be confronted by an attacker with a knife, despite all the news headlines you may see. You’re also around six times more likely to be hacked than be a victim of robbery.
According to a PwC study, 50% of UK respondents reported experiencing economic crime in the past two years, above the global average.
People need to pay as much attention to their digital security as they do for their personal security. How many of you open all the doors and windows before leaving the house or going to bed? That’s what a lot of internet users are doing when they ignore updates and set easy-to-guess passwords.
A survey by the National Cyber Security Centre (NCSC), released in April, found that “123456” was the most used password in Britain, followed by “123456789”, “qwerty” – the series of letters that appear in a line on a computer keyboard – “password” and “1111111”.
NCSC technical director Dr Ian Levy said: “Password re-use is a major risk that can be avoided. Nobody should protect sensitive data with something that can be guessed, like their first name, local football team or favourite band.”
We need to get rid of passwords because it’s a technology from 1964. How can we still be using them? It’s absurd
– Frank Abagnale, security expert
Guessing a simple password is just one way cybercriminals can steal a person’s data. Phishing scams attempt to lure you into revealing personal details by appearing to be from a legitimate company. Once the recipient of a phishing email or social media post clicks on a link in that correspondence, they are directed to an unsecure website. Criminals can then gain access to the victim’s computer or continue the fraud to request further personal details.
Malware, such as viruses, Trojans and spyware, are pieces of software that can damage devices and steal data. Victims download these harmful programs onto their computers after being duped into believing they contain something else.
The consequences of these criminal acts can be devastating. More than half of the most disruptive frauds in the UK last year resulted in losses of over £70,000, while around 24% saw the victims lose more than £700,000. Fraud also have a wider impact, too, as the proceeds often end up in the hands of organised criminals – often based abroad – funding a range of illegal activities from terrorism to human trafficking.
If the fraud happens at work, there is also the cost of investigation and remedial activities, disruption to other parts of the company and impact on the business’s reputation, relations and staff morale.
Juniper Research estimates that the cost of cybercrime to the global economy will reach $8 trillion by 2022.
Microsoft is helping people fight back by trying to end the era of passwords in favour of pin numbers and biometrics, such as fingerprints. Windows Hello, for example, uses facial recognition technology, letting users log in to their computer simply by looking at the camera above their screen. You can also use the feature to sign in to selected apps, including OneDrive and Dropbox. Windows Hello-supported devices use two cameras to create a 3D image of your face, including infrared radiation (IR) to prevent spoofing.
There is also password-less login via the Microsoft Authenticator app for the hundreds of thousands of Azure Active Directory connected apps that businesses use every day. Authenticator matches a number from the screen on your PC to one in the mobile app to confirm you are who you say you are. It also uses biometrics for a second layer of validation without a password. No one should protect their sensitive data with passwords, and using multi-factor authentication can protect you from 99.9% of attacks.
These new forms of authentication are called “hardware-enabled strong authentication”, which means that the biometric or PIN is tied to a specific device, so it would be very difficult and expensive for criminals to steal, because they would need the device and the biometric. Hackers can make more money faster if they focus on the low-hanging fruit of passwords.
Companies and organisations across the world are moving to more secure platforms.
NHS Scotland moved its computer systems to Windows 10 E5, which contains security features such as Advanced Threat Protection. The move will allow staff to respond to cyber-attacks in near-real-time thanks to behaviour sensors, security analysis in the cloud and threat intelligence.
NHS Wales, meanwhile, has given every public sector health worker in the country access to Microsoft 365 so they can securely share information. “It’s essential that NHS Wales has secure systems that health staff and patients trust, and this agreement will help achieve that,” said Andrew Griffiths, Director of NHS Wales Informatics Service.
Sian John, Microsoft UK’s Chief Security Advisor, helps companies safely and securely move to Azure. She has seen first-hand the issues that can arise when organisations incorrectly believe they can’t trust the cloud.
“The transition to cloud computing is speeding up in the UK, and part of that is transforming how companies look at security because a lot of data is stored in on-premise servers,” she said. “Some businesses try to fit the cloud into the way they already work, which can mean turning off certain Azure features. That could leave them less secure because they have less control over their digital estate.”

John explains that one of the big themes in cybersecurity today is identity, and people being able to log in to a system because they are who they say they are. For an IT department, the big questions are: Is an individual coming from the right IP address? Are they accessing what they’re allowed to access? Are they coming from a device that can be trusted? Do they use the same username and password for every website?
She said: “A lot of people use their corporate email as their main email account. So, when they register for a website, they enter their corporate email address and the same password. They are doing this on multiple sites. The other challenge is when people use their dog’s name or a sporting team as their password.”
The introduction of General Data Protection Regulation (GDPR) last year has encouraged companies in Europe to take security much more seriously. As the biggest change in data privacy regulation in two decades, GDPR is designed to harmonize data privacy laws across the continent, protect EU citizens’ data and reshape the way organisation approach data privacy.
Before GDPR, misuse of a person’s data was punishable by a fine of £500,000, leading to many firms opting to pay the levy rather than spend money overhauling their IT systems. Today, companies found guilty of misusing data could be hit with fines of up to €20 million, or 4% of the company’s annual turnover.
“GDPR has helped but we are all on a journey,” John said. “Cybersecurity needs to be built into a company’s wider risk profile; it shouldn’t be a special thing. If you’re a business leader at a company and you want to start a new project, you need to think about the opportunity, the financial risk, the operational risk. For some reason they always leave the cybersecurity risk to the IT team. It needs to be part of the overall conversation, how it can enable the business. Ultimately, if you look at most digital transformation, it needs to be done so the business can grow and thrive.”
Above all, you need to make security easy, John added. If logging on to a system and going through identity checks is difficult, people won’t do it. They will use their personal device, which might not have the right safeguards in place, to connect to their office.
Protecting our online environment is in everyone’s interest
– Brad Smith, Microsoft President
She points to Windows Hello as a great example of a product that’s secure and helps people be productive.
“It’s one of those products that’s actually more secure and easier to use than entering a password. If you force people to create more and more complex passwords, all you’re doing is making it harder to remember them, but it’s still relatively easy for a computer to crack it.”
In the US, where there is a much larger problem with fraud, one company is trying to encourage everyone to ditch passwords. Trusona, based in Arizona, was founded by Ori Eisen, who has been fighting online crime his entire career – either in anti-fraud roles at global firms or at one of the security businesses he has set up.
Running partly on Azure, Microsoft’s secure cloud platform, Trusona uses encrypted QR codes that change every 28 seconds to ensure secure access to anything from a website or cash machine to opening a bank account or getting a driving licence.
“When you go to a company’s website that’s using Trusona, there are no username or password boxes. There’s just a QR code,” Eisen said. “I open the Trusona app on my phone and go to the camera. I scan the on-screen QR code with my camera, which sends a message to my phone. I click ‘accept’ and it lets me into the site. My phone is the only one in the world that will get that message because it’s tied to a security certificate. There’s no username and no password. It even beats malware that logs keystrokes because I haven’t typed anything.”
The app is also aware of how you click the “accept” button, as a human could never do it the same over and over again. If this did happen, it must be a malicious program, and Trusona’s anti-replay technology would deny entry to the website.
“We are using the fact that people are just people to our advantage,” said Frank Abagnale, an advisor to Trusona, and one of the world’s leading experts on security. Abagnale was one of the world’s most wanted conmen 50 years ago, and his story provided the inspiration for Steven Spielberg’s 2002 film Catch Me If You Can, starring Leonardo DiCaprio as Abagnale and Tom Hanks as the FBI agent trying to stop him. After turning his back on crime, Abagnale has spent the past 40 years helping the FBI tackle theft, cybercrime and fraud, and advising major corporations on security. He estimates there is $900 billion of fraud in the US today.
“Fraud is everywhere, and it’s big. It’s certainly much more global than when I did it,” he said. “It used to be that criminals always had to be present to commit a crime. Now, you may know who’s committing the crime, you may have the address of the person in another country who’s doing it, but trying to get that person and convict them and bring them back to the country to be prosecuted is almost impossible.”
Abagnale also gives speeches on security across the world; and when he gets to the part about getting rid of passwords, the audiences always applaud. Security must move on, he believes, because criminals are relying on law enforcement staying the same.
“If I phone a company, all they can do is authenticate me by asking me questions,” he said. “The problem is, I can find the answer to almost every security question on the internet. I can get your mother’s maiden name, your date of birth, your wife’s maiden name, your children’s names, your dog’s name, I can find all that out. If you publish on social media where you’re born and your date of birth, I’m 98% of the way to stealing your identity. So, no matter what the company has asked me, I’m going to have the answer. Those questions are worthless, so we must move on. We need to get rid of passwords because it’s a technology from 1964. How can we still be using them? It’s absurd.
Eisen agreed: “We ask people who are not security experts to set passwords, and we wonder [why] the process is failing. Why aren’t we taking out the very thing that humans don’t want to do, which is remember long passwords?”
However, Abagnale and Eisen also point out that companies, governments and individuals are reluctant to abandon passwords. For most, it’s the only online security system they have known, and switching to on new technology requires a big leap of faith. The pair believe the day will come when passwords are consigned to the history books, but that will happen gradually, in a snowball effect, as one company switches over to a new system, then two, then five, then 10 etc.
“People don’t like change,” Abagnale said, before pointing out that security is far more critical for small businesses than for large corporations. “Last year, 42% of cyber breaches and hacks affected small businesses, but it’s much more important for an SME to protect themselves. If a big corporation has a forged cheque for $250,000 in the bank that someone doesn’t make good on, they have errors and omissions insurance. They pay a $50,000 deductible to their insurance company and get $200,000 back and they write it off as a loss. However, if you’re a small business, you’re out of business. I think a lot of companies have to be told that, because they think ‘it can’t happen to me’.”
Abagnale wants to see technology companies make their products as secure as they can, and then educate people on why they need to be safe online.
The best security measures are the ones that people don’t even need to think about, the ones that keep them safe but run silently in the background. Windows 10, for example, offers built-in and ongoing security protections, including Windows Defender Antivirus and a firewall, and automatically checks for the latest updates.
Elsewhere, Microsoft is helping businesses through Secure Score – the only dynamic report card for cybersecurity. By using it, organisations receive assessments and recommendations that typically reduce their chance of a breach by 30-fold. Microsoft Threat Protection brings together threat protection solutions across email, PCs, documents, identities and infrastructure into a single integrated experience in Microsoft 365, saving thousands of hours for over-stretched security teams.
The company’s Digital Crimes Unit (DCU) has worked with global law enforcement agencies to bring criminals to justice: to date, taking down 18 criminal bot-nets and rescuing nearly 500 million devices from secret bot-net control. In partnership with security teams across the company, the DCU has also tackled nation-state hackers, using innovative legal approaches to shut down 84 fake websites, often used in phishing attacks.
Meanwhile, Microsoft’s Defending Democracy programme is working to protect political campaigns from hacking, increase security of the electoral process, defend against disinformation and bring greater transparency to political advertising online. As part of this initiative, AccountGuard provides state-of-the-art cybersecurity protection at no extra cost to all candidates and campaign offices at the federal, state and local level, as well as think tanks and political organisations in the US. There are plans to extend the Defending Democracy programme to democracies around the world.
The topic is covered by Brad Smith in his new book, Tools and Weapons – The Promise and the Peril of the Digital Age.
Microsoft is continually developing tools that help protect individuals, companies and governments from cyber-criminals.
In A Call To Action: The Cyber Aware Perception Gap, Ben Wallace MP adds that “we will have most impact if we work together to bridge this dangerous perception gap, encouraging individuals to take simple actions to protect themselves, Britain, British people and British businesses. By speaking with ‘one voice’ to provide more consistent advice on the basic actions people should take to improve their online security, we can achieve real change.”
When it comes to cybersecurity, each of us is part of something larger than ourselves. Only by taking responsibility for our own digital activities – ensuring that we use official software that is fully up-to-date, accessing devices via biometric log-ins and fully understanding the risks from cyber criminals – will we make the UK the safest place to go online.