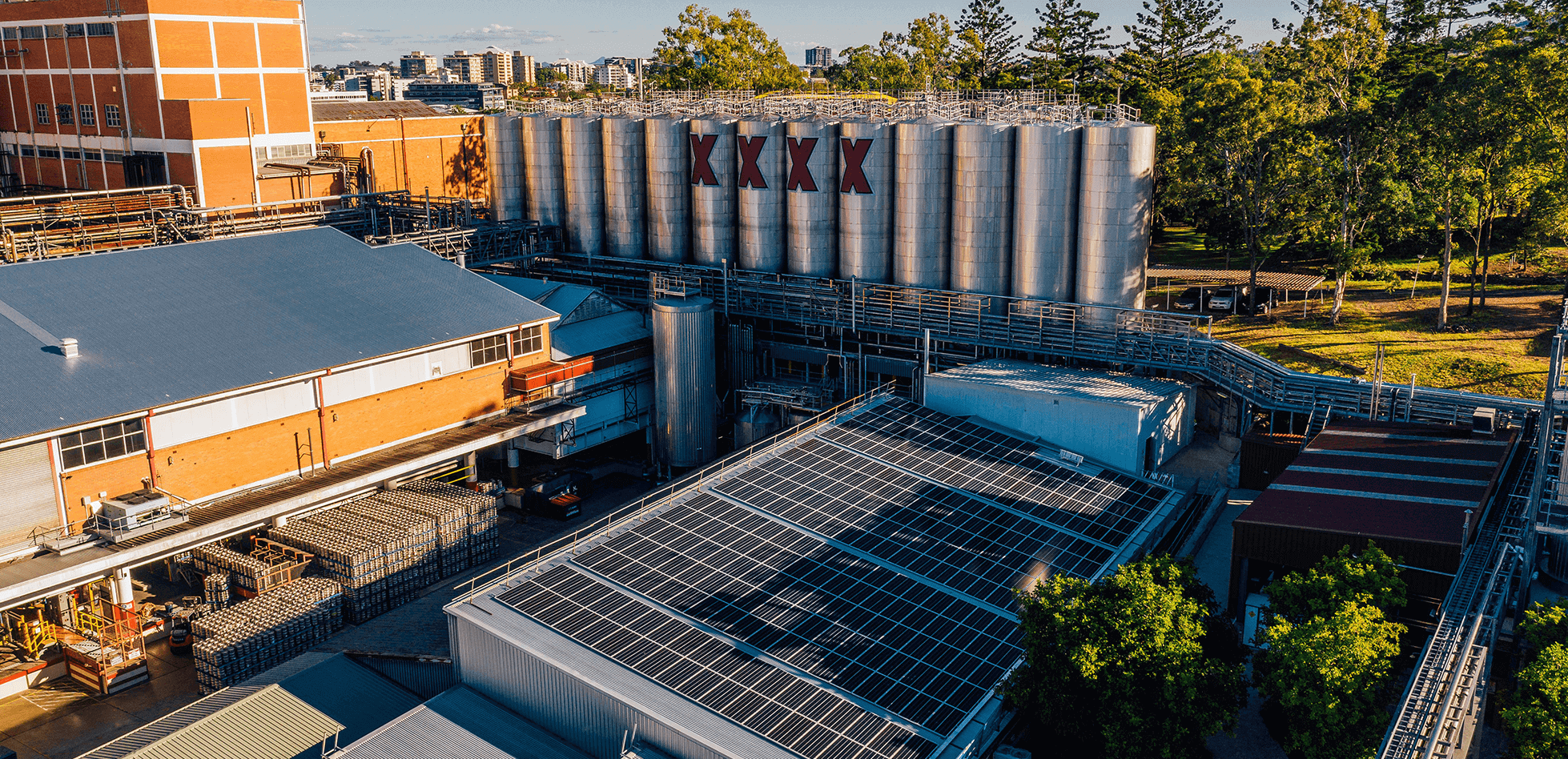
Lion serves up stronger data security to keep its supply chain moving
The ability to manufacture, distribute and sell is critical to the success of any supply-chain-driven organisation. It’s also imperative that organisations protect the technologies, systems and data used to power and support their supply chain.
This poses several challenges for people like Jamie Rossato, Chief Information Security Officer at Lion. Rossato leads a nimble team of cybersecurity experts at the leading beverage company, which employs almost 3,300 people in Australia, New Zealand and the United States.
“There are three major challenges I’m dealing with as a CISO [chief information security officer],” he says. “The first is the classic big data challenge – the volume, velocity and variety of the threats I have to deal with to protect the organisation. This requires me to think carefully around where resources are deployed.
“The second challenge is scarcity of time – time to engage with the business, my own people, our various technology providers, and industry peers and counterparts.
“And the third challenge is the dilemma of choice. We all have choices we need to make, but we need to do that with this increased complexity in data and with a small amount of time to make effective decisions to orient our security posture.”
“What we’re looking for is breadth of coverage, depth of coverage, and insights into incidents,” says Rossato. “We also want to make sure we’re following a well-defined process when dealing with incidents, because that allows us to move to automation.”
Rossato uses a cyberattack tool to test the effectiveness of his team’s security technologies in detecting the most likely threats. He also conducts quarterly reviews, which involves bringing in a group of cybersecurity professionals to carry out simulated attacks and penetration tests.
“This helps us determine how effective our preventative and detective controls are in identifying, containing and responding to these threats,” he says.
Improving Lion’s security posture with Microsoft
Lion relies on several Microsoft 365 E5 security solutions to help protect it from the increasingly frequent and sophisticated cyber threats that organisations face. These include capabilities across data security and information protection.
Microsoft Secure Score also provides Rossato and his team with an assessment of Lion’s security posture. It provides a numerical score on the organisation’s security situation, as well as recommendations on how to improve it. The score is based on a comparison of Lion’s settings and activities, with a security benchmark that Microsoft establishes from a combination of global security best practices.
“This has motivated and incentivised the team to do more with the tools they already have and continually improve our score every week,” explains Rossato. “The ability to see which security controls uplift our score is really powerful.”
It also enables Rossato to be better informed on whether Lion’s security controls are aligned with its risk appetite.
“It’s my role to ensure we’re operating within a set of parameters – informed by the threats, the effectiveness of our controls, and where the business is and wants to go – so that we continue to move forward and innovate with confidence,” he explains.
Lion’s partnership with Microsoft has enabled the company to strengthen its data governance and information security capabilities in key areas such as cloud access, data loss prevention and data discovery. The company has also been able to link these capabilities to its identity and access management capabilities in Entra.
“Being able to deploy and then iterate data controls with the various teams ensures we are able to sustainably lift our security posture without huge shocks to their way of operating,” says Rossato.
The value of stronger data governance and information security becomes something that the entire organisation gets behind, rather than just being seen as something our security team does.
Maximising the value of its technology investments
While Lion already uses a number of Microsoft’s security services to great effect, the organisation is always looking for ways to maximise the value of these investments. Rossato says the M365 roadmap is a great resource that helps him take full advantage of Lion’s M365 subscription.
“If you aren’t using the M365 roadmap, you’re missing out,” he says. “I look at that almost on a weekly basis to ensure we’re using the security controls available in the Microsoft shopping cart to the maximum extent.”
Combatting AI-powered cyber threats with AI-powered tools
Rossato sees an irrefutable trend towards the integration of artificial intelligence (AI) within organisations, likening it to the transformation brought about by the shift from typing pools to personal computers.
In accepting the inevitability of this shift, Lion’s CISO believes the cybersecurity function in organisations will need AI-powered tools to combat AI-powered threats.
“Security tools harnessing AI will – much like the evolution of word processing – enable faster, more accurate responses based on learnt patterns and iterative improvements to algorithms,” he explains.
“I expect, similar to auto-correct in documents, there will be times when the tools present a probable answer that actually isn’t the correct answer. But the 80/20 rule tells us that as long as we have trained personnel operating these tools, they will enable tasks to be completed to a higher quality more quickly and effectively over a sustained duration than a single operator could manage.
I always say the biggest challenge our security team has is dealing with threats coming at higher volumes and increasing velocity, and AI holds a promise to become a key tool in the cyber team’s arsenal of controls to deal with this.